By Dennis Schwarz, Axel F., and Brandon Murphy
Proofpoint researchers discovered an updated version of DanaBot in the wild. DanaBot is a banking/stealer malware first discovered by Proofpoint in May 2018. There have been at least three significant versions of the malware:
- Version 1: DanaBot – A new banking Trojan surfaces Down Under
- Version 2: DanaBot Gains Popularity and Targets US Organizations in Large Campaigns
- Version 3: ESET’s DanaBot updated with new C&C communication
This will be the fourth major update.
From May 2018 to June 2020, DanaBot was a fixture in the crimeware threat landscape. Proofpoint researchers observed multiple threat actors with at least 12 affiliate IDs in version 2 and 38 IDs in version 3. These affiliate identifications (IDs) represent the threat actors the DanaBot operators serve. Distribution has typically targeted financial institutions predominantly located in the United States, Canada, Germany, United Kingdom, Australia, Italy, Poland, Mexico, and Ukraine. After June 2020, there was a sharp decline in DanaBot activity in Proofpoint’s data and in public threat intel repositories (e.g. MalwareBazaar and #DanaBot). It disappeared from the threat landscape without a clear cause.
Starting in late October 2020, we observed a significant update to DanaBot samples appearing in VirusTotal. At the time of publication, Proofpoint researchers spotted two affiliate IDs using this latest version with at least one distribution method. While it has not returned to its former scale, DanaBot is malware that defenders should put back on their radar.
Malware Analysis
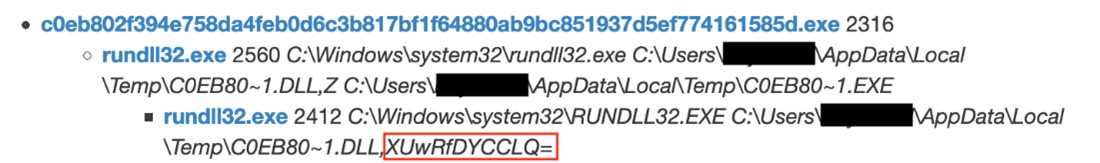
The sample with a SHA-256 hash of c0eb802f394e758da4feb0d6c3b817bf1f64880ab9bc851937d5ef774161585d was used for this analysis.
Like previous versions of DanaBot, version 4 is a large, multithreaded, modular malware written in the Delphi programming language. A loader component (EXE) decrypts, decompresses, and executes a secondary component (DLL) seen in Figure 1:
The secondary component removes the loader and reruns itself using a specially crafted export name highlighted above in red in Figure 1. The export name is base64 decoded and the first three bytes are subtracted from each other (i.e., running_mode = byte_0 – byte_1 – byte_2). This value determines the running mode of the secondary component, with four options available:
| Running Mode | Description |
| 0 | Main component |
| 1 | TOR component |
| 2 | Used for process injection of downloaded files |
| 3 | Module component |
This analysis will mostly focus on mode 0, the main component.
Anti-Analysis
Besides being written in Delphi there are a few other anti-analysis features in the malware:
- Some strings are constructed one character at a time (Figure 2)
- Some Windows API functions are resolved at run-time
- When a malware-related file is read or written to the filesystem, it is done in the middle of benign decoy file reads or writes
- Persistence is maintained by creating an LNK file that executes the main component in the user’s Startup directory. This file is only written once a WM_QUERYENDSESSION Windows event is received when the user logs off
Configuration
DanaBot’s configuration is hardcoded into a 356-byte structure (Figure 3):
Key configuration items are highlighted in red in Figure 3 and include the following:
Affiliate ID
As previously reported in DanaBot control panel revealed, we believe DanaBot is set up as a “malware as a service” in which one threat actor controls a global command and control (C&C) panel and infrastructure then sells access to other threat actors known as affiliates.
This field likely represents the ID of the affiliate associated with the sample. At the time of publication, only two IDs were found: 3 and 21. It is currently unclear whether version 4 affiliate IDs will overlap with previous version affiliate IDs, though they did change between versions 2 and 3.
Embedded Hash
It is currently unclear what the following embedded hash values represent:
- E1D3580C52F82AF2B3596E20FB85D9F4
- DE420A65BFC5F29167A85A5199065A0E
- E0ECDBB46B59DFAB6F7CB1136E7496F5
- 429B39BF421C0F74463EF2A17209ADAA
- 6266E79288DFE2AE2C2DB47563C7F93A
- DE6DF8FA2198DD77CFD93D89D8ECC62D
Version
This field below likely represents a version number that increments in newer samples:
- 1650
- 1701
- 1705
- 1732
- 1755
C&C IP Addresses and Ports
The IP addresses are hardcoded as DWORD values and are set to the following in the analyzed sample:
- 23[.]226.132.92
- 23[.]106.123.249
- 108[.]62.141.152
- 104[.]144.64.163
Version 3 of DanaBot mixed in decoy C&C addresses, but it does not appear version 4 is making use of them.
TOR
DanaBot has functionality to switch to TOR-based C&C. The analyzed sample contains the following hardcoded onion hostname:
- 5jjsgjephjcua63go2o5donzw5x4hiwn6wh2dennmyq65pbhk6qflzyd\.onion
Command and Control
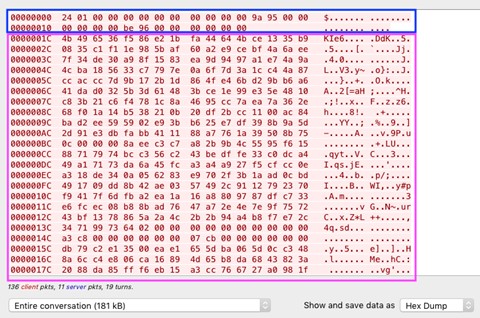
The C&C protocol in version 4 is similar to version 3. An example request is shown in Figure 4:
It is still a binary protocol using mostly TCP port 443. Requests and responses have a plaintext header (highlighted in blue in Figure 4) followed by command data (highlighted in purple). The header is 28-bytes and has the following fields:
| Offset | Size | Name | Notes |
| 0x00 | 8-bytes | Data length | |
| 0x08 | 4-bytes | Data compression/encryption mode | Four modes, described below |
| 0x0c | 8-bytes | Random value | |
| 0x14 | 8-bytes | Checksum | Value = data length + random value |
The command data structure is:
- AES-encrypted data
- Padding length (4-bytes)
- RSA-encrypted session key
- RSA Signature (in responses)
Depending on the command, data can be compressed using zlib (mode 1), ZIP (mode 2), or not compressed (modes 0 and 3).
Data is encrypted with AES-256 in CBC mode using a generated session key. In modes 0, 1, and 2, the session key is randomly generated and encrypted with RSA. For requests to the C&C server, an embedded public RSA key is used. For responses from the C&C server, a generated RSA key is used (see below). For mode 3, the session key is CryptDeriveKey’d based on the MD5 uppercase hex digest of the bot ID.
Responses from the C&C also contain an RSA signature which is verified using an embedded public RSA key.
The first request to the C&C server is a key exchange where an RSA key pair is generated by the malware, and the public key is sent to the C&C server. There is no response from the C&C for this request. Session keys used in future responses from the C&C server will be encrypted using this key.
The second request is an initial beacon to the C&C server. The data is a 479-byte structure containing:
| Offset | Size | Name | Notes |
| 0x00 | 4-bytes | Length | |
| 0x04 | 8-bytes | Random value | |
| 0x0C | 8-bytes | Checksum | Value = data length + random value |
| 0x14 | 4-bytes | Affiliate ID | See Configuration section above |
| 0x18 | 4-bytes | Command | Described below |
| 0x1c | 4-bytes | Sub-command | Described below |
| 0x20 | 4-bytes | Version | See Configuration section above |
| 0x24 | 4-bytes | Is admin flag | |
| 0x28 | 4-bytes | Process integrity level | |
| 0x2c | 4-bytes | Architecture | |
| 0x30 | 4-bytes | Windows version | Encoded into a DWORD value |
| 0x34 | 4-bytes | Time zone bias | |
| 0x38 | 36-bytes | Unknown null bytes | |
| 0x5c | 41-bytes | Bot ID | Prepended with string length and CRC32 value.
MD5 uppercase hex digest of hardware profile GUID |
| 0x85 | 41-bytes | Embedded hash value | Prepended with string length and CRC32 value.
See Configuration section above |
| 0xae | 41-bytes | Checksum 2 | Prepended with string length and CRC32 value.
MD5 uppercase hex digest of affiliate ID, bot ID, and embedded hash values concatenated together |
| 0xd7 | 41-bytes | MD5 uppercase hex digest of three random values | Prepended with string length and CRC32 value |
| 0x100 | remaining | Unknown null bytes |
Once decrypted (this particular response uses mode 0 and an extra layer of mode 3), the response from the C&C for the initial beacon is an echo of the request.
Other commands use similar structures but will not be detailed in this post.
Commands
Some of the main C&C commands we have identified include:
Command 1024, Sub-command 0
The initial beacon described in the C&C section above.
Command 2048, Sub-command 0
This command returns three hash values. It is unclear what the hashes are of, but they represent:
- Current set of “CommandRecord”s
- Current set of modules and/or files to download and execute
- Current set of “OnlineRec”s
Command 2048, Sub-command 1
Get updated list of C&C IP addresses.
Command 2048, Sub-command 2
This command returns a list of hash values. The hash values represent individual “CommandRecord”s.
Command 2048, Sub-command 3
This command is used to fetch a “CommandRecord”. These records map to three commands:
- Switch to TOR C&C communications
- Set C&C sleep value
- Enable the built-in stealer and system information components
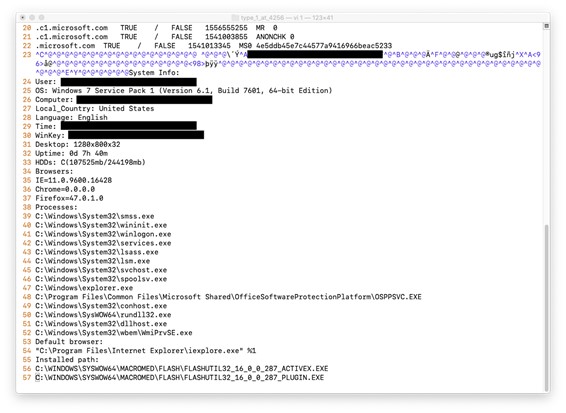
The stealer component steals credentials from various software such as web browsers and File Transfer Protocol (FTP) clients. The system information component collects system information seen below in Figure 5:
Command 2048, Sub-command 4
This command is used to send arbitrary data such as an initial screenshot and report from the stealer/system information components to the C&C server.
Command 2048, Sub-command 6
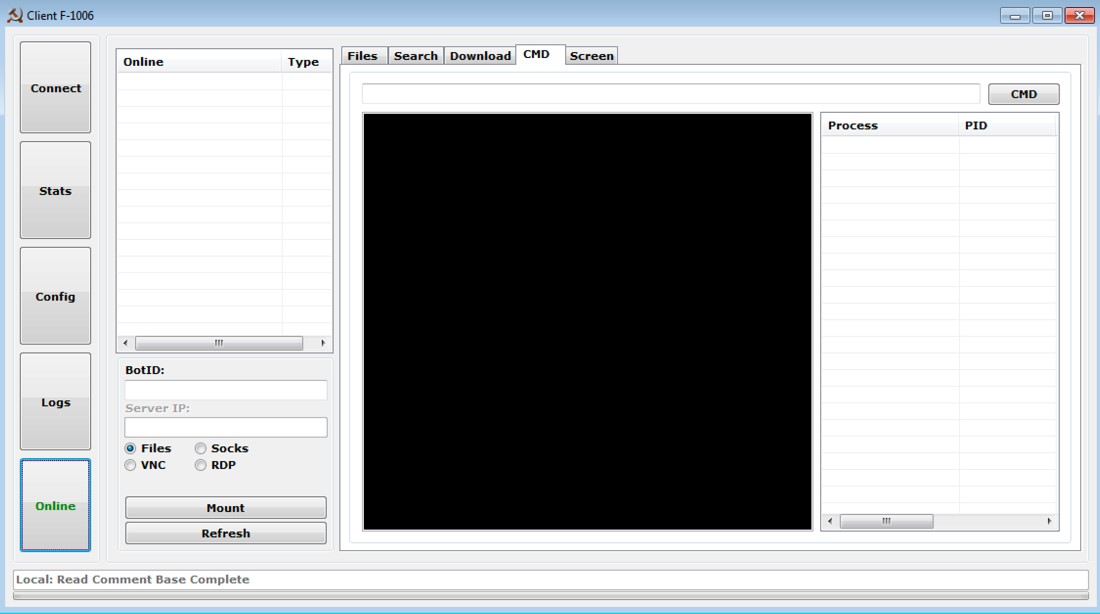
This command returns a set of “OnlineRec”s. Referencing our DanaBot control panel revealed blog post, these records seem to map to similar functionality accessible from the “Online” tab of the version 3 control panel seen below in Figure 6:
This includes functionality such as command shell, file system access, screen/keyboard/mouse access, and SOCKS proxy.
Command 2048, Sub-command 8
Note: all run modes detailed below reference the malware execution section above
This command returns a list of hashes. The hash values represent individual file records. File records are downloaded with command 2048, sub-command 9. File records are used to download files or modules to execute. Executable files can be run using:
- exe
- exe
- CreateProcess
- Process injection into secondary component using running mode 2
Modules are known as “MLocalProcess”s and are loaded into secondary components using run mode 3. They communicate with the main component over a localhost connection. At the time of publication, we have not seen any modules being distributed by the C&Cs. Based on previous versions of DanaBot, we suspect that the modules will enable the following functionality:
- Person-in-the-browser functionality along with web injects
- Video recording of the screen
- Keylogging
- VNC/RDP
Command 2048, Sub-command 10
Used to download TOR. The TOR client will be loaded into a secondary component using running mode 1.
Distribution Via Cracks Websites
Proofpoint researchers were able to narrow down at least one of the DanaBot distribution methods to various software warez and cracks websites that supposedly offer software keys and cracks for a free download, including anti-virus programs, VPNs, graphics editors, document editors, and games. However, the files distributed by these sites are a bundle of several different malware, including DanaBot.
A random file “600117809bae5__Adobe-Photoshop-CC-2211138-Crack-Incl-Keygen-X64-2021.zip” was downloaded and analyzed from one of the sites. It contained several “README” files and a password-protected archive containing the initial dropper for the malware bundle, “setup_x86_x64_install.exe.”
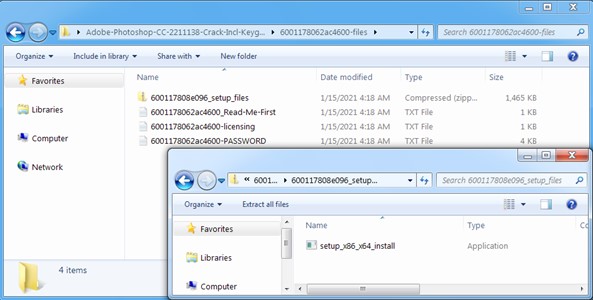
“Figure 9: A zip archive downloaded from a warez site containing the initial dropper for the malware bundle”
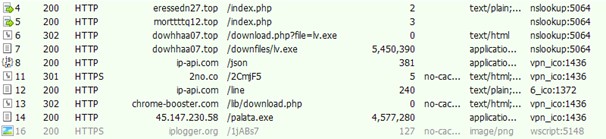
Running this executable generated the following traffic.
A brief description of this traffic and the malware components is below, but we have not conducted a full analysis of the files.
- Stage 1: drops and runs a stealer component and downloads stage 2
1.a. Stealer: the first two network requests, hxxp[:]//eressedn27[.]top/index.php and hxxp://morttttq12[.]top/index.php, belong to the stealer component. The stealer collects and uploads a zip with information about the infected machine, including:
- Browser’s information: saved username and password values, saved forms, credit card-related information, and cookies—from browsers including Chrome, Brave, Vivaldi, Opera, Avast, Firefox
- Screenshot: screenshot of the Desktop
- System Information: Operating System, language, keyboard languages, local time, username, CPU, RAM, video card, display resolution, installed software
- Cryptocurrency / wallets: we observed strings (but did not confirm exact functionality) related to cryptocurrency wallets and exchanges such as: Coinomi, waves-exchange, Ledger Live, Electrum, Electron Cash, Jaxx, Exodus, MultiBitHD, and Atomic.
1.b. Downloads stage 2: the following network request is a download of the next stage, “lv.exe”
- Stage 2: drops a miner and downloads DanaBot
2.a. Miner: a file is dropped (not analyzed) that appears to be an AutoIT cryptocurrency miner
2.b. Download DanaBot: DanaBot is downloaded from hxxp[:]//45.147.230[.]58/palata.exe
Research performed by CSIS (Center for Strategic and International Studies) appears consistent with the same actor that Proofpoint researchers found. CSIS described a different malware bundle that may include AZORult, Predator the Thief, Smoke Loader, Redline Stealer, Amadey, Ficker Stealer, and Raccoon Stealer. However, this is likely due to the involvement of a Traffic Direction System (TDS) serving different payloads depending on factors such as geographic location of the victim. The Indicators of Compromise (IOC) reported by CSIS included the domain chrome-booster[.]com which Proofpoint also observed in our network traffic screenshot (above) leading to the download of DanaBot via a 302 redirect. Finally, the CSIS research described the number of infections in hundreds of thousands in a span of approximately 1 month. The infections focused on quantity instead of quality and ranged across many countries including United States, Canada, India, Turkey, Brazil, and others.
Conclusion
For almost two years, DanaBot was one of the top banking malwares being used in the crimeware threat landscape. Multiple threat actors were distributing and using it to target financials in many countries. In the middle of 2020, DanaBot activity dropped off. Some of the affiliates that were using it have continued their campaigns using other banking malware (e.g. Ursnif and Zloader). It is unclear whether COVID-19, competition from other banking malware, redevelopment time, or something else caused the dip, but it looks like DanaBot is back and trying to regain its foothold in the threat landscape. We assess the number of DanaBot affiliates will grow and that DanaBot will once again be distributed via phishing campaigns within the next few months.
Indicators of Compromise
| Indicator | Type | Notes |
| c0eb802f394e758da4feb0d6c3b817bf1f64880ab9bc851937d5ef774161585d | SHA-256 | Analyzed sample, affiliate ID 3 |
| 23.226.132.92 | IP Address | C2 of analyzed sample |
| 23.106.123.249 | IP Address | C2 of analyzed sample |
| 108.62.141.152 | IP Address | C2 of analyzed sample |
| 104.144.64.163 | IP Address | C2 of analyzed sample |
| 5jjsgjephjcua63go2o5donzw5x4hiwn6wh2dennmyq65pbhk6qflzyd\.onion | Hostname | TOR C2 of analyzed sample |
| 83a67ecd166b919255b264718993c284a3238971a24c939c45e0c525f3361a43 | SHA-256 | Affiliate ID 21 |
| 149.129.212.179 | IP Address | C2 of affiliate ID 21 sample |
| 47.254.247.133 | IP Address | C2 of affiliate ID 21 sample |
| 159.89.114.62 | IP Address | C2 of affiliate ID 21 sample |
| 138.197.139.56 | IP Address | C2 of affiliate ID 21 sample |
| ab3c72aaacbe2c99646bf4d91e177585631b164f8cd9e9e5eb7a180ce7d945d5 | SHA-256 | 600117809bae5__Adobe-Photoshop-CC-2211138-Crack-Incl-Keygen-X64-2021.zip |
| ceb0ad27aaf97a5a33664f49aa107ca421c3f0a6e0b9a3c37f93455a258f3c04 | SHA-256
|
DanaBot downloaded from hxxp[:]//45.147.230[.]58/palata.exe |
Emerging Threats Signatures
ETPRO TROJAN Danabot Key Exchange Request
ETPRO TROJAN Danabot Command Beacon Request