
Check Point Research (CPR) has discovered new malware on Google’s Play Store that could spread through WhatsApp messages. The malware was designed with the ability to automatically respond to incoming WhatsApp messages on behalf of its victims, and the content of the response was provided by a remote server. CPR found the malware hidden in a fake “Netflix” application on Play Store called FlixOnline, which promised “unlimited entertainment” from anywhere in the world.
If successful, the malware enables its threat actors to perform a range of malicious activities, such as:
- Spread further malware via malicious links
- Steal credentials and data from users’ WhatsApp accounts
- Spread fake or malicious messages to users’ WhatsApp contacts and groups – for example, work-related groups
The malware was designed to be wormable, meaning it can spread from one Android device to another after the Android user clicks on the link in the message and downloads the malware.
How the Malware Works
- Victim installs the malware from Google’s Play Store
- The malware starts to “listen” for new notifications on WhatsApp
- Malware responds to every WhatsApp message the victim receives with a response crafted by the threat actors
- In this campaign, the response was a fake Netflix site that phished for credentials and credit card information
The Scripted WhatsApp Message
The malware sent the following automatic response to its victims incoming WhatsApp messages, attempting to lure others with the offer of a free Netflix service: “2 Months of Netflix Premium Free at no cost For REASON OF QUARANTINE (CORONA VIRUS)* Get 2 Months of Netflix Premium Free anywhere in the world for 60 days. Get it now HERE https://bit[.]ly/3bDmzUw”.
Disguised in a Fake “Netflix” Application

“Figure 1. “FlixOnline” Application on Google Play”
CPR found the malware hidden within an application on Google Play called ’FlixOnline.’” The app turned out to be a fake service that claims to allow users to view Netflix content from around the world on their mobiles. However, instead of allowing the mobile user to view Netflix content, the application is actually designed to monitor a user’s WhatsApp notifications, sending automatic replies to a user’s incoming messages using content that it receives from a remote server.
Responsible Disclosure and Victims
CPR responsibly disclosed its findings to Google. The malicious application was subsequently taken down by Google. Over the course of two months, the “FlixOnline” app was downloaded approximately 500 times. CPR has shared its research findings with WhatsApp, though there is no vulnerability on WhatsApp’s end.
Quote: Aviran Hazum, Manager of Mobile Intelligence at Check Point
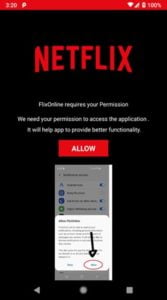
“Figure 2. “FlixOnline” Permissions Request”
“The malware’s technique is fairly new and innovative. The technique here is to hijack the connection to WhatsApp by capturing notifications, along with the ability to take predefined actions, like ‘dismiss’ or ‘reply’ via the Notification Manager. The fact that the malware was able to be disguised so easily and ultimately bypass Play Store’s protections raises some serious red flags. Although we stopped one campaign of the malware, the malware family is likely here to stay. The malware may return hidden in a different app.
Google Play Store’s protections can only go so far. Phone users need a mobile security solution. Luckily, we detected the malware early, and we quickly disclosed it to Google – who also acted quickly. Users should be wary of download links or attachments that they receive via WhatsApp or other messaging apps, even when they appear to come from trusted contacts or messaging groups. If you think you’re a victim, I would immediately remove the application from my device, and proceed to change all my passwords.”
Security Tips for Android Users
- Install a security solution on your device
- Download applications only from official markets
- Keep your device and apps up to date
For more information visit: https://research.checkpoint.com/2021/new-wormable-android-malware-spreads-by-creating-auto-replies-to-messages-in-whatsapp/






