Sophos has released its annual State of Ransomware 2024 survey report, which found that the average ransom payment has increased by 297% in the last year.
Australian organisations that paid the ransom reported an average payment of USD6 million, up from USD1.51 million in 2023 and more than USD2 million above the global average (USD3.96 million). However, ransoms are just one part of the cost. Excluding ransoms, the survey found the average recovery cost for Australian organisations reached USD2.37 million, an increase of more than USD500,000 from the USD1.72 million recovery cost Sophos reported last year.
Despite the soaring ransoms, this year’s survey indicates a considerable reduction in the rate of ransomware attacks, with 54% of Australian organisations being hit (59% globally), compared with 70% of Australian organisations in 2023 and 80% in 2022. While the propensity to be hit by ransomware increases with revenue, even the smallest organisations (less than USD10 million in revenue) are still regularly targeted, with just under half (47%) hit by ransomware in the last year.
The 2024 report also found that 76% of ransom demands made towards Australian organisations were for USD1 million or more, with the average ransom demand being USD6.8 million, suggesting ransomware operators are seeking huge payoffs. Unfortunately, these increased ransom amounts are not just for the highest-revenue organisations surveyed. Nearly half (46%) of global organisations with revenue of less USD50 million received a seven-figure ransom demand in the last year.
Sophos says its data for the State of Ransomware 2024 report came from a vendor-agnostic survey of 5,000 cybersecurity and IT leaders based in 14 countries across the Americas, EMEA, and Asia-Pacific, conducted between January and February 2024. Three hundred thirty Australian respondents feature in the report. Organisations surveyed had between 100 and 5,000 employees, and revenue ranged from less than USD10 million to more than USD5 billion.
“We must not let the slight dip in attack rates give us a sense of complacency,” said Sophos Field CTO John Shier. “Ransomware attacks are still the most dominant threat today and fuel the cybercrime economy. Without ransomware, we would not see the same variety and volume of precursor threats and services that feed into these attacks. The skyrocketing costs of ransomware attacks belie the fact that this is an equal-opportunity crime. The ransomware landscape offers something for every cybercriminal, regardless of skill. While some groups are focused on multi-million-dollar ransoms, there are others that settle for lower sums by making it up in volume.”
Compromised credentials were the most common root cause of an attack for Australian organisations, used in 37% of incidents. This was followed by exploited vulnerabilities, used in 32% of attacks. This is in line with in-the-field incident response findings from Sophos’ most recent Active Adversary report. With 49% of attacks leading to data encryption, it is worrying that 66% of Australian organisations that had data encrypted paid the ransom – the second highest rate reported by any country surveyed. This an increase from both last year’s rate of 53% and the 2024 global average of 56%.
Other notable findings from the report include:
- Australian organisations are getting slower at recovering from attacks, with 36% fully recovered in up to a week, down from 46% in 2023. 33% took between one and six months, a significant increase on the 17% last year;
- The average ransom payment for Australian organisations came in at 101% of the initial ransom demand received;
- 58% of Australian organisations that had data encrypted used multiple recovery methods to get data back, above the global average of 47%;
- 84% of Australian organisations hit by ransomware in the past year said that the cybercriminals attempted to compromise their backups during the attack. In 66% of instances, backup compromise attempts were successful, the highest rate of any country; and
- In 20% of incidents where data was encrypted, data was also stolen – a slight increase from last year’s 17% but still below the global average of 32%.
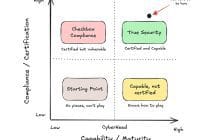
“The two most common root causes of ransomware attacks, exploited vulnerabilities and compromised credentials, are preventable, yet still plague too many organisations,” said Shier. “Businesses need to critically assess their levels of exposure to these root causes and address them immediately. In a defensive environment where resources are scarce, it’s time organisations impose costs on the attackers. Only by raising the bar on what’s required to breach networks can organisations hope to maximise their defensive spend.”
You can read the full report here.