Written By Mustafa Hamid, Global Discipline Lead, Modern Workforce, Dell Technologies Consulting Services.
The average cost of a data breach worldwide last year was 4.24 million U.S. dollars. Phishing and firmware attacks are on the rise, half a million password attacks occur daily and ransomware is a continuous threat for every business. The significance of the issue, reflected in the amount of resources, staff and money organisations are devoting to cybersecurity, cannot be overstated.
Dell Technologies says it is introducing new products and services focused on the Zero Trust cybersecurity model, by now introducing Identity & Endpoint Protection with Microsoft Zero Trust.
What is Zero Trust?
Let’s take a step back. Zero Trust is a cybersecurity architecture that shifts how organisations approach security from reliance solely on perimeter defenses to a proactive strategy that allows only known-good activity across ecosystems and data pipelines.
The Zero Trust model enforces trust across devices, users, networks, applications, infrastructure and data with automation and orchestration across the modern workplace stack and leverages analytics and visibility to provide insights.
Zero Trust follows the guiding principles of:
- Verify explicitly — always verify users, devices and network requests based on every available data point regardless of their location
- Use least privileged access — limit user access to the resources they absolutely need for their current role and job functions
- Assume breach — segment access, leverage end-to-end encryption, and continuously look for threats and ways to strengthen defenses
Instead of assuming everything within the network perimeter can be trusted, Zero Trust continuously authenticates every device and entity, verifies behavior is explicitly allowed, and ensures actions are understood and monitored. A thoughtful implementation of Zero Trust principles, leveraging both the right strategy and modern security tools, is needed so as not to hinder productivity in a hybrid work environment.
Dell Identity & Endpoint Protection with Microsoft Zero Trust
The path to Zero Trust looks different for every organisation and it is a complex journey to implement this architecture. Dell is committed to simplifying the adoption of Zero Trust by streamlining integration across IT environments.
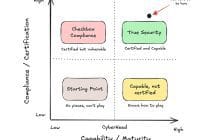
No matter where an organisation is on their Zero Trust journey, it is important to establish where they stand, measure progress as they go, prioritise efforts that maximise business impact and instill a security mindset throughout their organisation.
Dell created an accelerated approach to protecting Microsoft ecosystems using Zero Trust principles, Microsoft solutions and our security expertise. Our Identity & Endpoint Protection with Microsoft Zero Trust services are designed to quickly help organisations understand their current security posture and priorities to achieve Zero Trust alignment, then provide the expert guidance, implementation services, adoption and change management strategies to drive secure outcomes.
This new suite of service offerings helps organisations:
- Assess their environment to gauge existing cybersecurity posture and provide actionable recommendations and insights to make progress toward Zero Trust alignment, including assessment of Active Directory and Azure Active Directory.
- Secure the computing landscape through the lens of Zero Trust. For organisations that rely heavily on Microsoft technology, the Microsoft Defender suite of solutions along with Dell services help secure key defense focus areas such as endpoints, Microsoft 365 and Active Directory, and provide integration with the Microsoft Sentinel SIEM platform and IT Services Management platforms, such as ServiceNow.
- Ensure end-users are invested in the need for security controls and have the knowledge and ability to participate in helping secure their environment. Our approach includes adoption and change management specifically centered on cyber solutions to drive awareness and training, and instill a security mindset with end-users.
- Provide continuous protection with incident response and managed detection and response services for customers needing managed services for cybersecurity.